This set of MCQ(multiple choice questions) focuses on the Foundations of Cryptography NPTEL Week 8 Assignment Solutions.
Course Layout (Answers Link)
- Week 1: Assignment answers
- Week 2: Assignment answers
- Week 3: Assignment answers
- Week 4: Assignment answers
- Week 5: Assignment answers
- Week 6: Assignment answers
- Week 7: Assignment answers
- Week 8: Assignment answers
- Week 9: Assignment answers
- Week 10: Assignment answers
- Week 11: Assignment answers
- Week 12: Assignment answers
NOTE: You can check your answer immediately by clicking show answer button. Moreover, this set of “Foundations of Cryptography NPTEL Week 8 Assignment Solution” contains 05 questions.
Now, start attempting the quiz.
Foundations of Cryptography NPTEL Week 8 Assignment Solutions
Q1. Choose the right option(s) for the authenticate-then-encrypt approach which is instantiated with a CPA-secure encryption scheme and an SCMA-secure MAC:
a) It is CCA-secure but not an authenticated encryption scheme
b) It does not provide ciphertext integrity
c) It provides ciphertext integrity
d) It is not CCA-secure
Answer: b), d)
Q2. In the key-exchange problem, the goal of the sender and receiver is to:
a) Agree upon a common public key, over a private channel
b) Agree upon a fixed common key, over a public channel
c) Agree upon a fixed common key, over a private channel
d) Agree upon a random common key, over a public channel
Answer: d)
Q3. Which of the following is/are sufficient to build an authenticated encryption scheme?
a) A block cipher
b) A PRG
c) A hash function
d) All of these
Answer: a), b)
Q4.

a) The above MAC is randomized and hence is SCMA-secure
b) The above MAC is deterministic and hence is CMA-secure
c) The above MAC when used in the encrypt-then-authenticate approach leads to an authenticated encryption scheme
d) The above MAC when used in the encrypt-and-authenticate approach leads to an authenticated encryption scheme
Answer: a), b), c), d)
Q5.
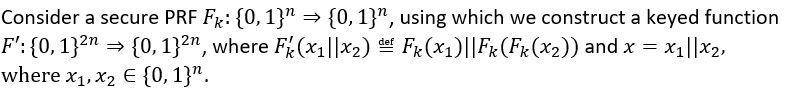
a) Function F’ is not a secure PRF
b) Function F’ is a secure PRF
c) Function F’ when used directly leads to a CMA-secure MAC
d) Function F’ when used directly does not lead to a CMA-secure MAC
Answer: a), d)
<< Prev- Foundations of Cryptography NPTEL Week 7 Solutions
>> Next- Foundations of Cryptography NPTEL Week 9 Solution
DISCLAIMER: Use these answers only for the reference purpose. Quizermania doesn't claim these answers to be 100% correct. So, make sure you submit your assignments on the basis of your knowledge.For discussion about any question, join the below comment section. And get the solution of your query. Also, try to share your thoughts about the topics covered in this particular quiz.
